Sigue el log...SystemParametersInfo(SPI_GETDRAGFULLWINDOWS,4) [c:\windows\system32\drwtsn32.exe]
SystemParametersInfo(SPI_GETHIGHCONTRAST,12) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\dwwin.exe) [c:\windows\system32\dwwin.exe]
FreeLibrary(C:\WINDOWS\system32\msv1_0.dll) [c:\windows\system32\dwwin.exe]
OpenProcessToken(C:\WINDOWS\system32\drwtsn32.exe) [c:\windows\system32\drwtsn32.exe]
SystemParametersInfo(SPI_GETNONCLIENTMETRICS,500) [c:\windows\system32\drwtsn32.exe]
SystemParametersInfo(SPI_GETMENUDROPALIGNMENT,0) [c:\windows\system32\drwtsn32.exe]
SystemParametersInfo(SPI_GETMOUSEHOVERTIME,0) [c:\windows\system32\drwtsn32.exe]
SystemParametersInfo(SPI_GETFLATMENU,0) [c:\windows\system32\drwtsn32.exe]
GetModuleHandle(LPK.DLL) [c:\windows\system32\drwtsn32.exe]
OpenProcess(drwtsn32.exe) [c:\windows\system32\drwtsn32.exe]
GetModuleHandle(USER32) [c:\windows\system32\drwtsn32.exe]
LoadLibrary(imm32.dll) [c:\windows\system32\drwtsn32.exe]
CreateEvent(Global\userenv: User Profile setup event) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\lz32.dll) [c:\windows\system32\drwtsn32.exe]
ResumeThread() [c:\windows\system32\drwtsn32.exe]
LoadLibrary(ntdll.dll) [c:\windows\system32\drwtsn32.exe]
CreateEvent(DbgEngEvent_00000550) [c:\windows\system32\drwtsn32.exe]
LoadLibrary(rpcrt4.dll) [c:\windows\system32\drwtsn32.exe]
GetComputerName() [c:\windows\system32\drwtsn32.exe]
AdjustTokenPrivileges(SE_PRIVILEGE_ENABLED) [c:\windows\system32\drwtsn32.exe]
OpenProcess(HxD.exe) [c:\windows\system32\drwtsn32.exe]
VirtualAllocEx(c:\documents and settings\r32\mis documentos\tools\hxd\hxd.exe,MEM_RESERVE,PAGE_READWRITE) [c:\windows\system32\drwtsn32.exe]
VirtualAllocEx(c:\documents and settings\r32\mis documentos\tools\hxd\hxd.exe,MEM_COMMIT,PAGE_READWRITE) [c:\windows\system32\drwtsn32.exe]
WriteProcessMemory(c:\documents and settings\r32\mis documentos\tools\hxd\hxd.exe) [c:\windows\system32\drwtsn32.exe]
CreateFile(C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\drwtsn32.log) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\kernel32.dll) [c:\windows\system32\drwtsn32.exe]
LoadLibrary(c:\windows\system32\exts.dll) [c:\windows\system32\drwtsn32.exe]
LoadLibrary(c:\windows\system32\ntsdexts.dll) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\documents and settings\r32\mis documentos\tools\hxd\hxd.exe) [c:\windows\system32\drwtsn32.exe]
GetModuleHandle(ntdll.dll) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1848) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1900) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1836) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1832) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1676) [c:\windows\system32\drwtsn32.exe]
Sleep(0) [c:\windows\system32\drwtsn32.exe]
GetUserName() [c:\windows\system32\drwtsn32.exe]
LoadLibrary(secur32.dll) [c:\windows\system32\drwtsn32.exe]
QuerySystemInformation() [c:\windows\system32\drwtsn32.exe]
OpenProcess(System) [c:\windows\system32\drwtsn32.exe]
OpenProcess(smss.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\smss.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(csrss.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(winlogon.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\winlogon.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(services.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\services.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(lsass.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\lsass.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(VBoxService.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\vboxservice.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(svchost.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\svchost.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(SbieSvc.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\sandboxie\sbiesvc.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(explorer.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\explorer.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(VBoxTray.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\vboxtray.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(ctfmon.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\ctfmon.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(alg.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(XueTr.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\documents and settings\r32\mis documentos\tools\xuetr\xuetr.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(u1210.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\documents and settings\r32\mis documentos\tools\red\u1210.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(iexplore.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\internet explorer\iexplore.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(firefox.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\mozilla firefox\firefox.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(BSA.EXE) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\documents and settings\r32\mis documentos\descargas\bsa\bsa.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(sniff_hit.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\idefense\map\sniff_hit.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(wireshark.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\wireshark\wireshark.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(dumpcap.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\wireshark\dumpcap.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(SbieCtrl.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\sandboxie\sbiectrl.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(procexp.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\documents and settings\r32\mis documentos\tools\procexp.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(wmiprvse.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(SandboxieRpcSs.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\sandboxie\sandboxierpcss.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(SandboxieDcomLaunch.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\archivos de programa\sandboxie\sandboxiedcomlaunch.exe) [c:\windows\system32\drwtsn32.exe]
OpenProcess(winsa64.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\sandbox\r32\defaultbox\drive\c\windows\winsa64.exe) [c:\windows\system32\drwtsn32.exe]
ReadProcessMemory(c:\windows\system32\drwtsn32.exe) [c:\windows\system32\drwtsn32.exe]
TerminateProcess(à?¤\dee\harskvol1\do) [c:\windows\system32\drwtsn32.exe]
CreateFile(C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\user.dmp) [c:\windows\system32\drwtsn32.exe]
LoadLibrary(psapi.dll) [c:\windows\system32\drwtsn32.exe]
CreateToolhelp32Snapshot(TH32C2_SNAPALL,964) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1648) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1644) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1640) [c:\windows\system32\drwtsn32.exe]
SuspendThread(1636) [c:\windows\system32\drwtsn32.exe]
FreeLibrary() [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\ntdll.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\USER32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\GDI32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\IMM32.DLL) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\ADVAPI32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\RPCRT4.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\Secur32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\OLEAUT32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\msvcrt.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\ole32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\VERSION.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\WinSxS\x86_Microsoft.Windows.Common-Controls_6595b64144ccf1df_6.0.2600.6028_x-ww_61e65202\comctl32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\SHLWAPI.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\SHELL32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\WINMM.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\UxTheme.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\psapi.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\MSACM32.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\DBGHELP.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\exts.dll) [c:\windows\system32\drwtsn32.exe]
FreeLibrary(C:\WINDOWS\system32\ntsdexts.dll) [c:\windows\system32\drwtsn32.exe]
GetModuleHandle(mscoree.dll) [c:\windows\system32\drwtsn32.exe]
ExitProcess(0) [c:\windows\system32\drwtsn32.exe]
GetModuleHandle(EXPLORER.EXE) [c:\windows\system32\drwtsn32.exe]
GetModuleHandle(C:\WINDOWS\system32\Msctf.dll) [c:\windows\winsa64.exe]
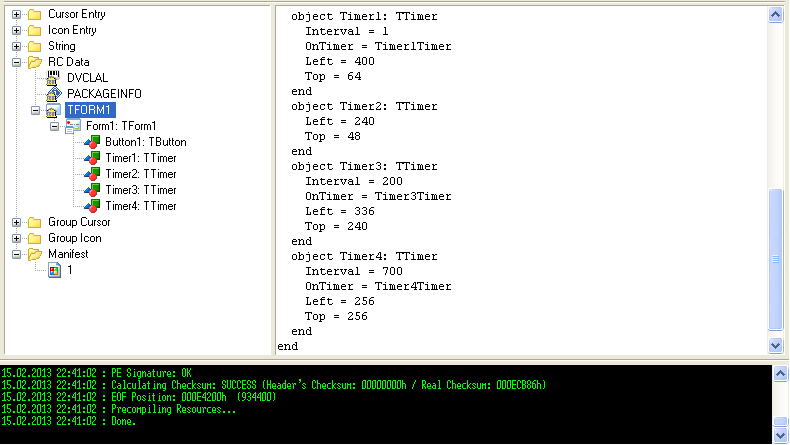
Report generated with Buster Sandbox Analyzer 1.85 at 12:31:20 on 08/02/2013
[ General information ]
* File name: c:\documents and settings\r32\escritorio\infect3d\comprovante\winsa64.exe
[ Changes to filesystem ]
* Creates file C:\WINDOWS\winsa64.cfg
* Creates file C:\WINDOWS\winsa64.exe
* Creates file C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\drwtsn32.log
* Creates file C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\user.dmp
* Modifies file C:\Documents and Settings\r32\Configuración local\Archivos temporales de Internet\Content.IE5\index.dat
* Modifies file C:\Documents and Settings\r32\Configuración local\Historial\History.IE5\index.dat
* Modifies file C:\Documents and Settings\r32\Cookies\index.dat
[ Changes to registry ]
* Modifies value "NumberOfCrashes=00000003" in key HKEY_LOCAL_MACHINE\software\microsoft\DrWatson
old value "NumberOfCrashes=00000002"
* Modifies value "NukeOnDelete=00000001" in key HKEY_LOCAL_MACHINE\software\microsoft\Windows\CurrentVersion\Explorer\BitBucket
old value empty
* Creates value "DisableNotifications=00000001" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile
* Creates value "DisableNotifications=00000001" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\PublicProfile
* Modifies value "DisableNotifications=00000001" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile
old value empty
* Empties value "EnableFirewall" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile
old value "EnableFirewall=00000001"
* Modifies value "ProxyEnable=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings
old value empty
* Creates value "ProxyServer=3100320037002E0030002E0030002E0031003A0039003600360036000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings
binary data=127.0.0.1:9666
* Modifies value "ProxyOverride=3100320037002E0030002E0030002E0031000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings
binary data=127.0.0.1
old value "ProxyOverride=6C006F00630061006C000000"
binary data=local
* Creates Registry key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012013020720130208
* Creates Registry key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012013020820130209
* Modifies value "SavedLegacySettings=46000000B9010000030000000E0000003132372E302E302E313A39363636090000003132372E302E302E3100000000040000000000000050EB206AFBFACD01010000000A00020F000000000000000000000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections
old value "SavedLegacySettings=46000000BA0100000100000000000000050000006C6F63616C00000000040000000000000050EB206AFBFACD01010000000A00020F000000000000000000000000"
* Creates value "winsa64=43003A005C00570049004E0044004F00570053005C00770069006E0073006100360034002E006500780065000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Run
binary data=C:\WINDOWS\winsa64.exe
[ Network services ]
* Looks for an Internet connection.
* Queries DNS "www.cadastramento.net".
* Queries DNS "www.chabvf.info".
* Queries DNS "www.yoeqtxutb.info".
* Queries DNS "www.itjdcryfa.info".
* Queries DNS "solutionfinder.microsoft.com".
* Queries DNS "s3.amazonaws.com".
* Queries DNS "google.es".
* Queries DNS "www3.nationalgeographic.com".
* Queries DNS "google.bg".
* Queries DNS "google.net".
* Queries DNS "google.co.uk".
* Queries DNS "google.kz".
* Queries DNS "google.pt".
* Queries DNS "google.by".
* C:\WINDOWS\winsa64.exe Connects to "212.1.208.24" on port 80 (TCP - HTTP).
* Downloads file from "www.cadastramento.net/sistema.html".
[ Process/window/string information ]
* Enables process privileges.
* Gets user name information.
* Gets system default language ID.
* Gets computer name.
* Checks for debuggers.
* Creates a mutex "CTF.LBES.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.Compart.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.Asm.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.Layouts.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.TMD.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.TimListCache.FMPDefaultS-1-5-21-1482476501-1202660629-1957994488-1003MUTEX.DefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Anti-Malware Analyzer routine: WinDbg detection.
* Anti-Malware Analyzer routine: Sandboxie detection.
* Creates an event named "ShellCopyEngineRunning".
* Creates an event named "ShellCopyEngineFinished".
* Creates a mutex "INSONIA".
* Creates a mutex "HxD{73025671-91B6-473C-B0EE-6EAB6FD0E6DE}".
* Creates a mutex "MSCTF.Shared.MUTEX.EBH".
* Opens a service named "AudioSrv".
* Creates a mutex "MidiMapper_modLongMessage_RefCnt".
* Creates a mutex "MidiMapper_Configure".
* Enumerates running processes.
* Creates process "(null),C:\WINDOWS\system32\dwwin.exe -x -s 456,C:\WINDOWS\system32".
* Injects code into process "c:\windows\system32\dwwin.exe".
* Creates a mutex "SHIMLIB_LOG_MUTEX".
* Creates a mutex "Local\_!MSFTHISTORY!_".
* Creates a mutex "Local\c:!documents and settings!r32!configuración local!archivos temporales de internet!content.ie5!".
* Creates a mutex "Local\c:!documents and settings!r32!cookies!".
* Creates a mutex "Local\c:!documents and settings!r32!configuración local!historial!history.ie5!".
* Creates a mutex "RasPbFile".
* Lists all entry names in a remote access phone book.
* Opens a service named "RASMAN".
* Opens a service named "Sens".
* Injects code into process "c:\windows\system32\drwtsn32.exe".
* Creates an event named "DbgEngEvent_00000550".
* Injects code into process "c:\documents and settings\r32\mis documentos\tools\hxd\hxd.exe".
* Terminates process "à?¤\dee\harskvol1\do".
* Contains string Anubis detection routine found ("76487-337-8429955-22614")
* Contains string Sandboxie detection routine found ("SbieDll.dll")
Extrayendo información de mis sistema:
Code:
Report generated with Buster Sandbox Analyzer 1.85 at 12:31:20 on 08/02/2013
Detailed report of suspicious malware actions:
Anubis detection routine found
Checked for debuggers
Created a mutex named: CTF.Asm.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003
Created a mutex named: CTF.Compart.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003
Created a mutex named: CTF.Layouts.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003
Created a mutex named: CTF.LBES.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003
Created a mutex named: CTF.TimListCache.FMPDefaultS-1-5-21-1482476501-1202660629-1957994488-1003MUTEX.DefaultS-1-5-21-1482476501-1202660629-1957994488-1003
Created a mutex named: CTF.TMD.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003
Created a mutex named: HxD{73025671-91B6-473C-B0EE-6EAB6FD0E6DE}
Created a mutex named: INSONIA
Created a mutex named: Local\_!MSFTHISTORY!_
Created a mutex named: Local\c:!documents and settings!r32!configuración local!archivos temporales de internet!content.ie5!
Created a mutex named: Local\c:!documents and settings!r32!configuración local!historial!history.ie5!
Created a mutex named: Local\c:!documents and settings!r32!cookies!
Created a mutex named: MidiMapper_Configure
Created a mutex named: MidiMapper_modLongMessage_RefCnt
Created a mutex named: MSCTF.Shared.MUTEX.EBH
Created a mutex named: RasPbFile
Created a mutex named: SHIMLIB_LOG_MUTEX
Created file in defined folder: C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\drwtsn32.log
Created file in defined folder: C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\user.dmp
Created process: (null),C:\WINDOWS\system32\dwwin.exe -x -s 456,C:\WINDOWS\system32
Defined file type created in Windows folder: C:\WINDOWS\winsa64.exe
Defined registry AutoStart location created or modified: machine\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile\DisableNotifications = 00000001
Defined registry AutoStart location created or modified: machine\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\PublicProfile\DisableNotifications = 00000001
Defined registry AutoStart location created or modified: machine\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\DisableNotifications = 00000001
Defined registry AutoStart location created or modified: user\current\software\Microsoft\Windows\CurrentVersion\Run\winsa64 = 43003A005C00570049004E0044004F00570053005C00770069006E0073006100360034002E006500780065000000
File copied itself
Firewall settings change: machine\system\currentcontrolset\services\sharedaccess\parameters\firewallpolicy\standardprofile\enablefirewall = empty value key
Got computer name
Got system default language ID
Got user name information
Internet connection: C:\WINDOWS\winsa64.exe Connects to "212.1.208.24" on port 80 (TCP - HTTP)
Listed all entry names in a remote access phone book
Modified file in defined folder: C:\Documents and Settings\r32\Configuración local\Archivos temporales de Internet\Content.IE5\index.dat
Modified file in defined folder: C:\Documents and Settings\r32\Configuración local\Historial\History.IE5\index.dat
Modified file in defined folder: C:\Documents and Settings\r32\Cookies\index.dat
Queried DNS: google.bg
Queried DNS: google.by
Queried DNS: google.co.uk
Queried DNS: google.es
Queried DNS: google.kz
Queried DNS: google.net
Queried DNS: google.pt
Queried DNS: s3.amazonaws.com
Queried DNS: solutionfinder.microsoft.com
Queried DNS: www.cadastramento.net
Queried DNS: www.chabvf.info
Queried DNS: www.itjdcryfa.info
Queried DNS: www.yoeqtxutb.info
Queried DNS: www3.nationalgeographic.com
Sandboxie detection routine found
Terminated process: à?¤\dee\harskvol1\do
Transfered files from and/or to internet
Report generated with Buster Sandbox Analyzer 1.85 at 12:31:20 on 08/02/2013
[ General information ]
* File name: c:\documents and settings\r32\escritorio\infect3d\comprovante\winsa64.exe
[ Changes to filesystem ]
* Creates file C:\WINDOWS\winsa64.cfg
* Creates file C:\WINDOWS\winsa64.exe
* Creates file C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\drwtsn32.log
* Creates file C:\Documents and Settings\All Users\Datos de programa\Microsoft\Dr Watson\user.dmp
* Modifies file C:\Documents and Settings\r32\Configuración local\Archivos temporales de Internet\Content.IE5\index.dat
* Modifies file C:\Documents and Settings\r32\Configuración local\Historial\History.IE5\index.dat
* Modifies file C:\Documents and Settings\r32\Cookies\index.dat
[ Changes to registry ]
* Modifies value "NumberOfCrashes=00000003" in key HKEY_LOCAL_MACHINE\software\microsoft\DrWatson
old value "NumberOfCrashes=00000002"
* Modifies value "NukeOnDelete=00000001" in key HKEY_LOCAL_MACHINE\software\microsoft\Windows\CurrentVersion\Explorer\BitBucket
old value empty
* Creates value "DisableNotifications=00000001" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile
* Creates value "DisableNotifications=00000001" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\PublicProfile
* Modifies value "DisableNotifications=00000001" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile
old value empty
* Empties value "EnableFirewall" in key HKEY_LOCAL_MACHINE\system\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile
old value "EnableFirewall=00000001"
* Modifies value "ProxyEnable=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings
old value empty
* Creates value "ProxyServer=3100320037002E0030002E0030002E0031003A0039003600360036000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings
binary data=127.0.0.1:9666
* Modifies value "ProxyOverride=3100320037002E0030002E0030002E0031000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings
binary data=127.0.0.1
old value "ProxyOverride=6C006F00630061006C000000"
binary data=local
* Creates Registry key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012013020720130208
* Creates Registry key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012013020820130209
* Modifies value "SavedLegacySettings=46000000B9010000030000000E0000003132372E302E302E313A39363636090000003132372E302E302E3100000000040000000000000050EB206AFBFACD01010000000A00020F000000000000000000000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections
old value "SavedLegacySettings=46000000BA0100000100000000000000050000006C6F63616C00000000040000000000000050EB206AFBFACD01010000000A00020F000000000000000000000000"
* Creates value "winsa64=43003A005C00570049004E0044004F00570053005C00770069006E0073006100360034002E006500780065000000" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Run
binary data=C:\WINDOWS\winsa64.exe
[ Network services ]
* Looks for an Internet connection.
* Queries DNS "www.cadastramento.net".
* Queries DNS "www.chabvf.info".
* Queries DNS "www.yoeqtxutb.info".
* Queries DNS "www.itjdcryfa.info".
* Queries DNS "solutionfinder.microsoft.com".
* Queries DNS "s3.amazonaws.com".
* Queries DNS "google.es".
* Queries DNS "www3.nationalgeographic.com".
* Queries DNS "google.bg".
* Queries DNS "google.net".
* Queries DNS "google.co.uk".
* Queries DNS "google.kz".
* Queries DNS "google.pt".
* Queries DNS "google.by".
* C:\WINDOWS\winsa64.exe Connects to "212.1.208.24" on port 80 (TCP - HTTP).
* Downloads file from "www.cadastramento.net/sistema.html".
[ Process/window/string information ]
* Enables process privileges.
* Gets user name information.
* Gets system default language ID.
* Gets computer name.
* Checks for debuggers.
* Creates a mutex "CTF.LBES.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.Compart.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.Asm.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.Layouts.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.TMD.MutexDefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Creates a mutex "CTF.TimListCache.FMPDefaultS-1-5-21-1482476501-1202660629-1957994488-1003MUTEX.DefaultS-1-5-21-1482476501-1202660629-1957994488-1003".
* Anti-Malware Analyzer routine: WinDbg detection.
* Anti-Malware Analyzer routine: Sandboxie detection.
* Creates an event named "ShellCopyEngineRunning".
* Creates an event named "ShellCopyEngineFinished".
* Creates a mutex "INSONIA".
* Creates a mutex "HxD{73025671-91B6-473C-B0EE-6EAB6FD0E6DE}".
* Creates a mutex "MSCTF.Shared.MUTEX.EBH".
* Opens a service named "AudioSrv".
* Creates a mutex "MidiMapper_modLongMessage_RefCnt".
* Creates a mutex "MidiMapper_Configure".
* Enumerates running processes.
* Creates process "(null),C:\WINDOWS\system32\dwwin.exe -x -s 456,C:\WINDOWS\system32".
* Injects code into process "c:\windows\system32\dwwin.exe".
* Creates a mutex "SHIMLIB_LOG_MUTEX".
* Creates a mutex "Local\_!MSFTHISTORY!_".
* Creates a mutex "Local\c:!documents and settings!r32!configuración local!archivos temporales de internet!content.ie5!".
* Creates a mutex "Local\c:!documents and settings!r32!cookies!".
* Creates a mutex "Local\c:!documents and settings!r32!configuración local!historial!history.ie5!".
* Creates a mutex "RasPbFile".
* Lists all entry names in a remote access phone book.
* Opens a service named "RASMAN".
* Opens a service named "Sens".
* Injects code into process "c:\windows\system32\drwtsn32.exe".
* Creates an event named "DbgEngEvent_00000550".
* Injects code into process "c:\documents and settings\r32\mis documentos\tools\hxd\hxd.exe".
* Terminates process "à?¤\dee\harskvol1\do".
* Contains string Anubis detection routine found ("76487-337-8429955-22614")
* Contains string Sandboxie detection routine found ("SbieDll.dll")
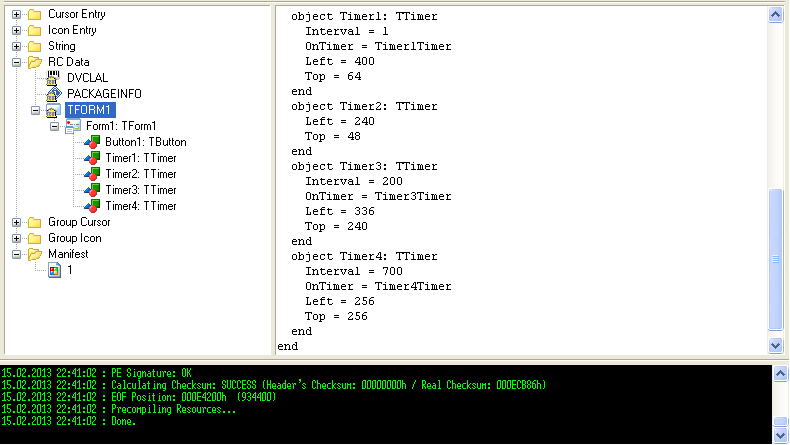
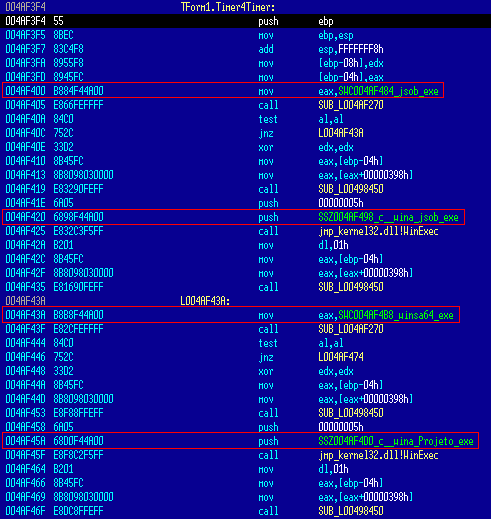
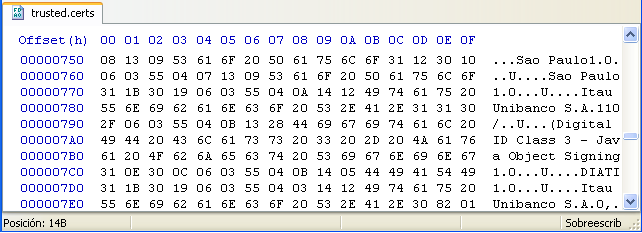
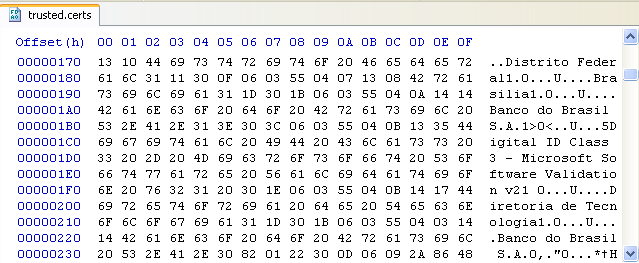
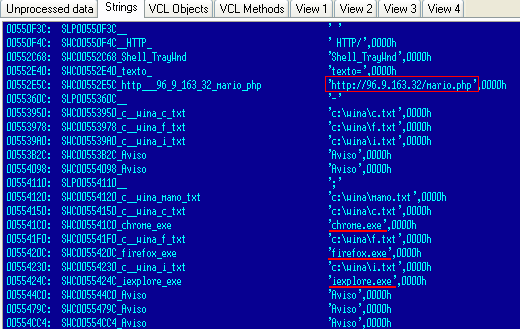
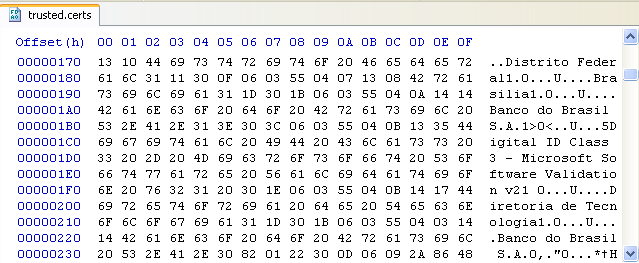
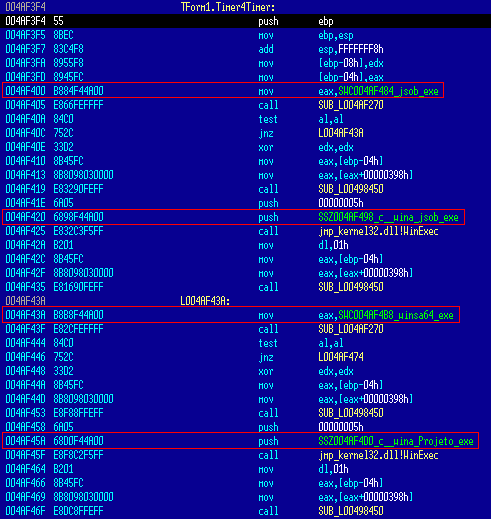 Captura de los certificados válidos para los siguente bancos de Brasil:
Captura de los certificados válidos para los siguente bancos de Brasil: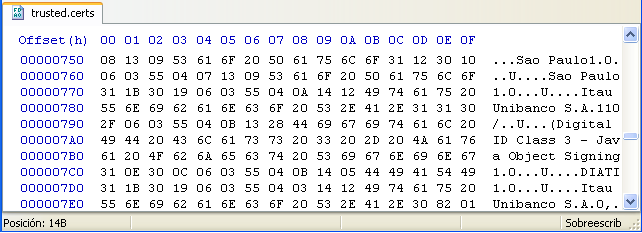
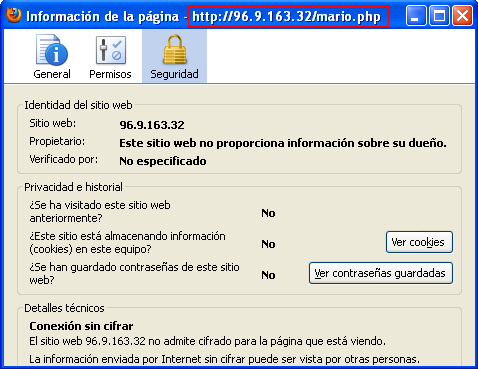
 Conexión con servidor (independientemente del explorador...):
Conexión con servidor (independientemente del explorador...):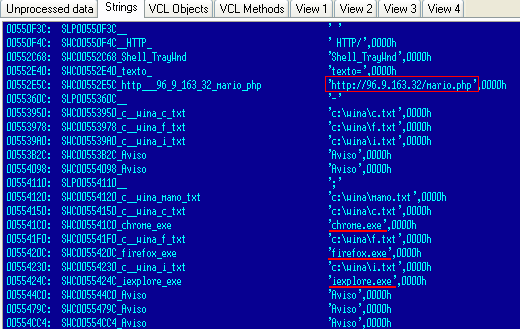 El archivo "mario.php" estaba vacio, ni iframe ni código:
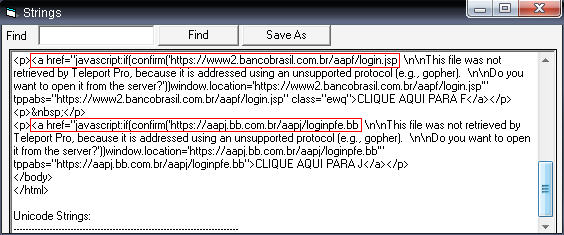
El archivo "mario.php" estaba vacio, ni iframe ni código: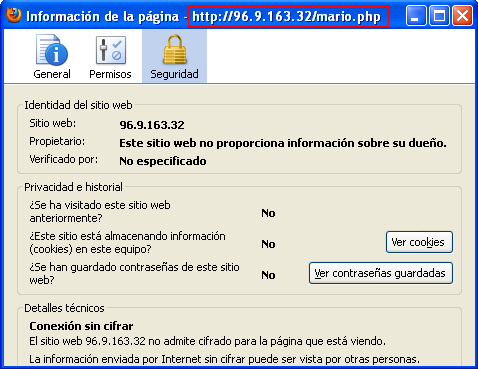 Buscando archivos en su servidor encuentro este html, con refréncia a dos bancos:
Buscando archivos en su servidor encuentro este html, con refréncia a dos bancos: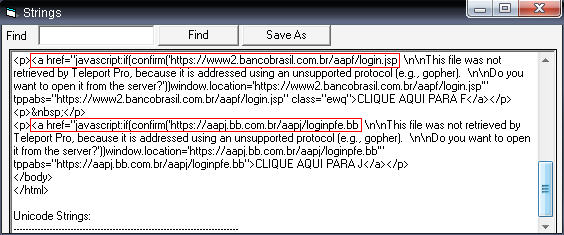 Podría haber sacado mucha más información si lo hubiese ejecutado en máquina real, aborta conexiones y creación de algunos archivos en preséncia de entorno virtual.
Podría haber sacado mucha más información si lo hubiese ejecutado en máquina real, aborta conexiones y creación de algunos archivos en preséncia de entorno virtual.